As he forms a team to investigate Godzilla and Anguirus set out to help defeat the invaders. Respawn EntertainmentはApex Legendsエーペックスレジェンズへ品質の改善とバグ修正を含むアップデートを配信しました 品質改善アップデート ランクマッチでのマッチメイキング時にプレイヤーがランダムに準備完了にならない問題を解決 アニメーションバナーのポーズでハ.
ある日突然やってくる Ddos 攻撃の概要と対策 Yamory Blog
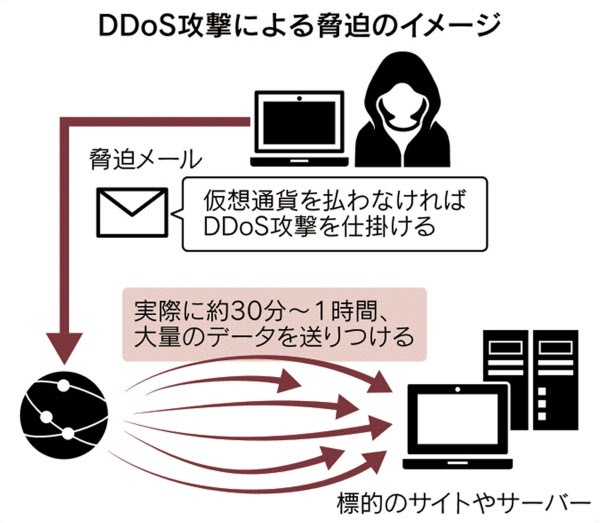
Ddos恐喝 相次ぐ サイト標的に金銭要求メール 日本経済新聞

Ddos攻撃対策サービス Inap Japan
Denial-of-Service DoS Imagine youre sitting in traffic on a one-lane country road with cars backed up as far as the eye can see.
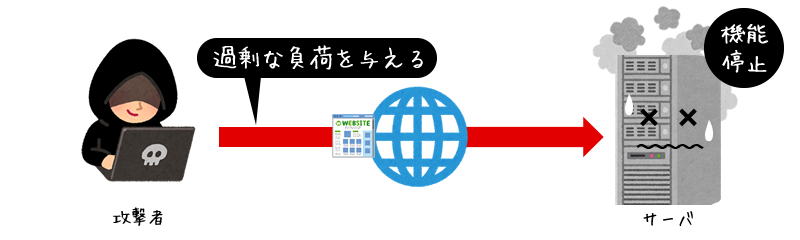
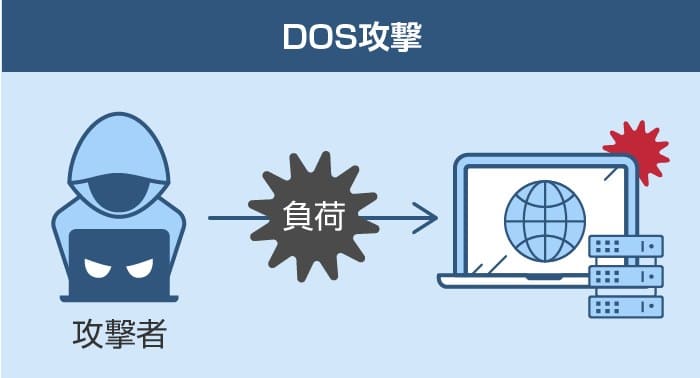
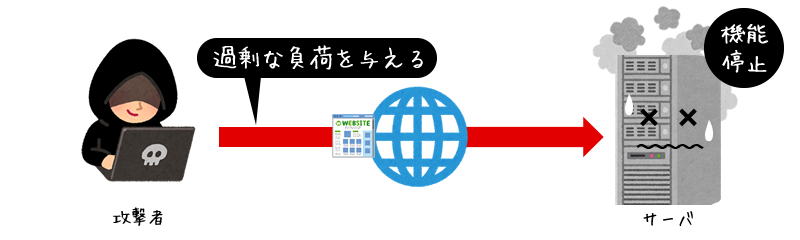
Dos攻撃tぽは. In computing a denial-of-service attack DoS attack is a cyber-attack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to the InternetDenial of service is typically accomplished by flooding the targeted machine or resource with superfluous requests in an attempt to. The next example is a denial-of-service attack against any Java application that allows deserialization. Taking the time to learn the ins and outs of the most common types of.
Sybil Attack is a type of attack seen in peer-to-peer networks in which a node in the network operates multiple identities actively at the same time and undermines the authoritypower in. In order to use the WikiLeaks public submission system as detailed above you can download the Tor Browser Bundle which is a Firefox-like browser available for Windows Mac OS X and GNULinux and pre-configured to connect using the. Episode II - Attack of the Clones.
A hash collisionThis is in contrast to a preimage attack where a specific target hash value is specified. If you dont have line of sight to the opponent at the start of your turn you cant charge that opponent. A denial-of-service DoS attack occurs when legitimate users are unable to access information systems devices or other network resources due to the actions of a malicious cyber threat actor.
As a WordPress user safeguarding your site from security attacks should be of the utmost importance. Cybercriminals typically use it to extract data that they can leverage over victims for financial gain. You cant take a 5-foot step in the same round as a charge.
4 月 1 日から文部科学省の Web サイトが見られなくなる ブラウザにおける TLS10 TLS11 の廃止. Symantec Endpoint Protectionが頻繁にポートスキャン攻撃をログに記録しましたと表示してくるのでなぜこんなことになるのかについて関連する情報を調べてみました 目次1. Respawn Entertainmentは同社開発の基本無料プレイオンライン対戦シューターApex Legendsについていくつかの問題を修正したことを明らかにしました 今回発表された修正内容はランク戦でのマッチメイキング時におけるフリーズ問題やDos攻撃への対策強化アリーナでのグ.
When deserializing this root object the JVM will begin creating a recursive object graph. That data can range from financial data. Standing up takes more effort.
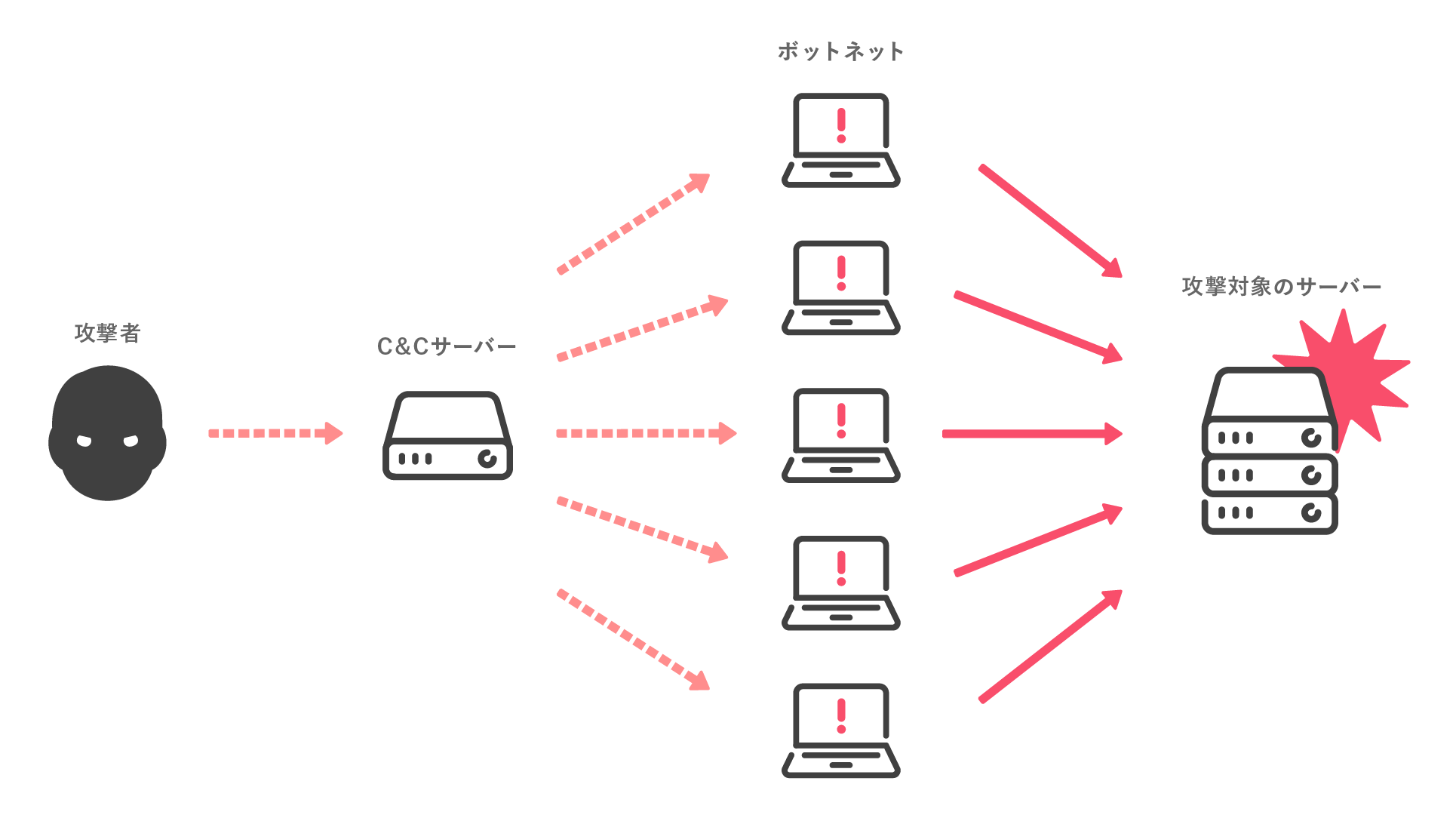
DDoS attack Distributed Denial of Service attack 分散型サービス妨害攻撃 上記DoS攻撃にはインターネットプロトコルの特性を攻略してネットワークに接続されたコンピュータに過剰な負荷をかけてサービスを提供することをできなくしてしまう種類の攻撃がある. WordPress powers nearly 35 percent of the internet making it a major target for cybercriminals. Services affected may include email websites online accounts eg banking or other services that rely on the affected computer or network.
Normally this road never sees more than a car or two but a county fair and a major sporting event have ended around the same time. The HashSet called root in the following code sample has members that are recursively linked to each other. Movable Type の XMLRPC API に OS コマンドインジェクションの脆弱性攻撃時の影響大.
There are roughly two types of collision attacks. Doing so costs an amount of movement equal to half your speed. For example if your speed is 30 feet you must spend 15 feet of movement to stand up.
A manga artist becomes suspicious of his employers when a garbled message is discovered on tape. In cryptography a collision attack on a cryptographic hash tries to find two inputs producing the same hash value ie. With Ewan McGregor Natalie Portman Hayden Christensen Christopher Lee.
Malware is a catch-all term for any type of malicious software designed to harm or exploit any programmable device or network. Dream Moods is the only free online source you need to discover the meanings to your dreams. An iFixit teardown of Apples 24 M1 iMac in which we cross our fingers and hope this thing isnt as iPad-like as it looks.
What is a denial-of-service attack. Ten years after initially meeting Anakin Skywalker shares a forbidden romance with Padmé Amidala while Obi-Wan Kenobi investigates an assassination attempt on the senator and discovers a secret clone army crafted for the Jedi. Directed by George Lucas.
You cant stand up if you dont have enough movement left or if your speed is 0. Contribute to cywebhammer development by creating an account on GitHub. Published May 24 2021.
If you are able to take only a standard action on your turn you can still charge but you are only allowed to move up to your speed instead of up to double your speed and you cannot draw a weapon unless you possess the. To move while prone you must crawl or use magic such as teleportation. Tor is an encrypted anonymising network that makes it harder to intercept internet communications or see where communications are coming from or going to.
Directed by Jun Fukuda Yoshimitsu Banno Ishirô Honda Shûe Matsubayashi. これまで 生産管理の仕事というと どうしても受け身の仕事と考えられてきました 曰く当社の営業は予測が当たらなくって困る 曰くいつもお客様は無理難題を言ってくる 曰く設計はなかなか図面を出さないがそれが原因で手配が間に合わなくても最後に怒られるの. Collision attack Find two different messages m 1 and m 2 such that hashm 1 hashm 2.
Check out our ever expanding dream dictionary fascinating discussion forums and other interesting topics related to dreaming. Hammer DDos Script - Python 3. With Hiroshi Ishikawa Yuriko Hishimi Minoru Takashima Tomoko Umeda.

Ddos攻撃とは 対策方法 Dos攻撃との違い おすすめ対処サービス 図解 ボクシルマガジン

Ddos攻撃 Ddos攻撃を詳しく解説 キーワード解説 Hh News Reports ハミングヘッズ
Ddos攻撃のためにすべき4つの対策方法 被害事例も合わせて解説 セキュマガ Lrm株式会社が発信する情報セキュリティの専門マガジン
Dos攻撃対策サービス セコム
Ddos攻撃とは 読み方 目的や事例 対策方法を解説 サイバーセキュリティ Com
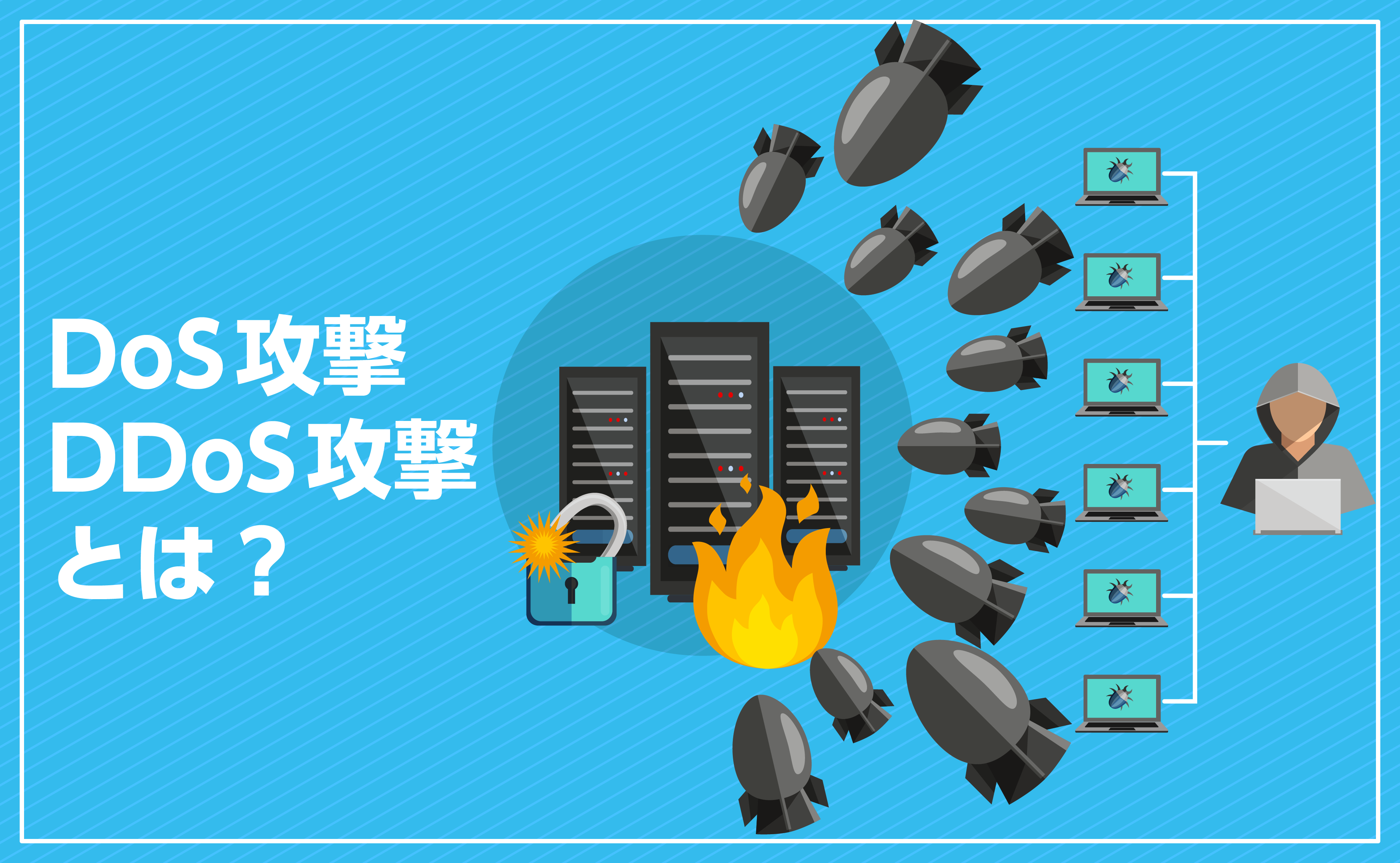
Dos攻撃 Ddos攻撃とは 意味と対策方法をわかりやすく解説 クラウド型waf 攻撃遮断くん
Ddos攻撃
Ddos攻撃 コピー機 複合機のリース Acnコピー機
